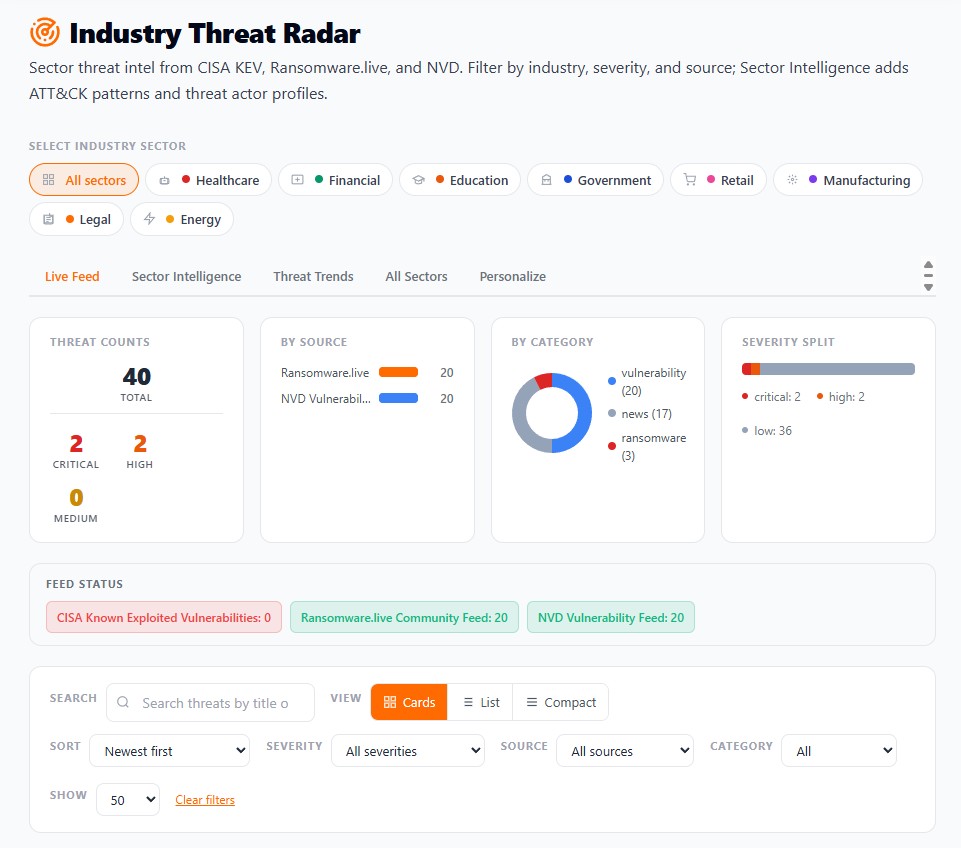
Know your ransomware exposure before disruption forces the issue.
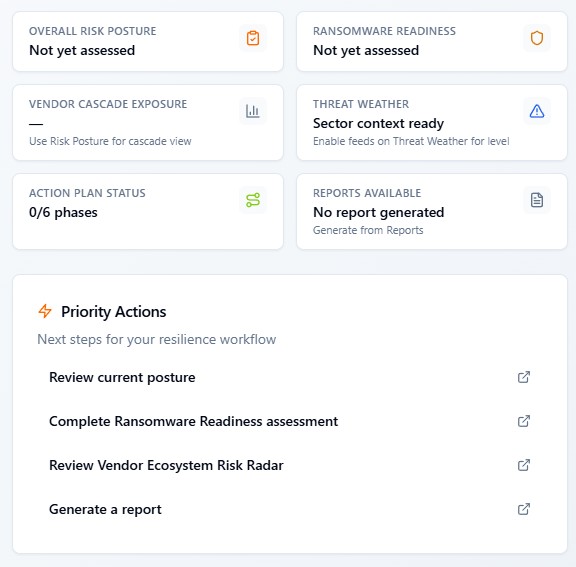
Run a focused risk review in minutes. Surface posture gaps, sector threat pressure, and the actions you should prioritize first.
Your sector, assets, and third parties-in one view.
Act now-so an incident doesn't decide for you.
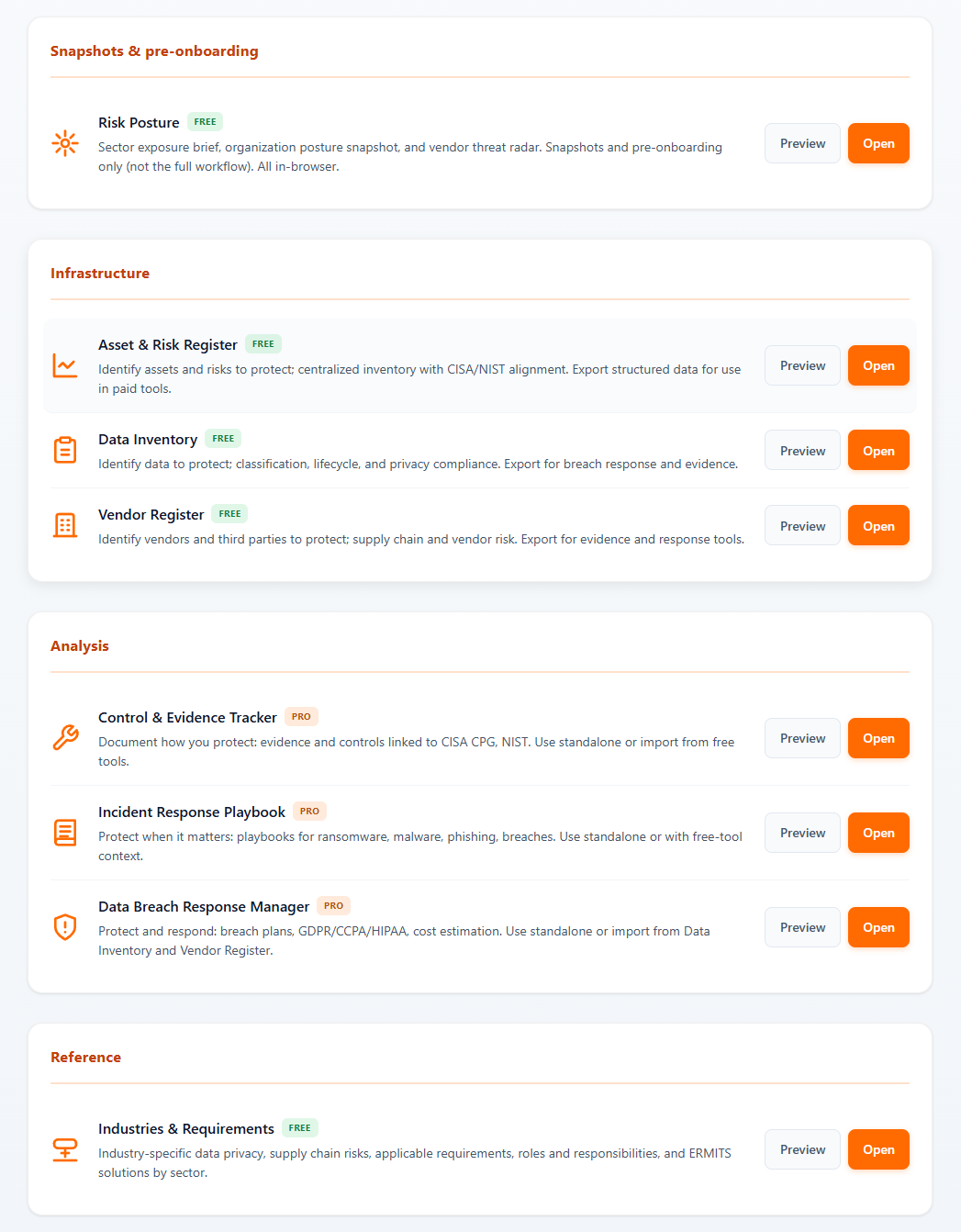
What you get fast
- -Exposure snapshot across posture, threat, and resilience
- -High-priority gaps and likely disruption pressure
- -Clear next actions for leadership and operations
- -A prioritized posture snapshot before the workspace
About 3 minutes